Linux chkrootkit is a tool that can help you detect if your system has been compromised by a rootkit. A rootkit is a malicious software that hides itself from detection and gives an attacker full control over your system. Linux chkrootkit scans your system for common signs of rootkit infection, such as hidden files, processes, ports, modules, and hooks.
Chkrootkit also checks for specific rootkits, such as lrk, t0rn, Ambient, and RST. Linux chkrootkit is not a replacement for antivirus software, but rather a complementary tool that can increase your security awareness.
To begin installation of chkrootkit, follow this procedure:
-
First, log in to your server and download the C/C++ compilers and libraries required for the package to work using the following command:
yum groupinstall 'Development Tools'
-
Next, transition to the directory /usr/local/bin/ using the following command:
cd /usr/local/bin/
-
Now, download the chkrootkit tarball (Archived Installation) to the server using this command:
wget ftp://ftp.chkrootkit.org/pub/seg/pac/chkrootkit.tar.gz
*NOTE: this link can change, so make sure to check the URL below for the “Source tarball”
https://www.chkrootkit.org/download/
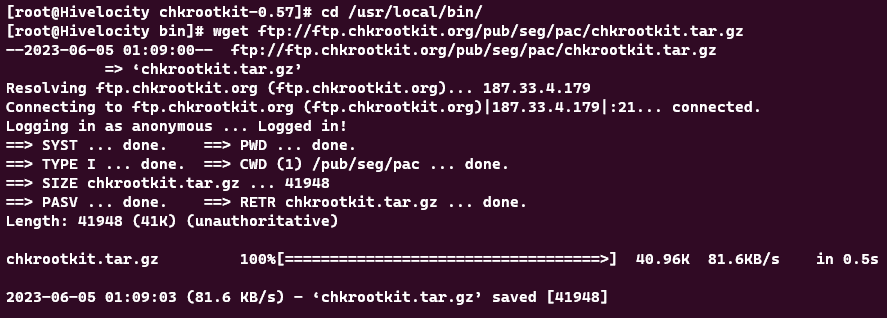
*NOTE: If encountering an error involving “==> PASV … couldn’t connect to 187.33.4.179 port 53755: Connection refused” or any of that sort, proceed to add the mentioned IP in the error you’ve received to the allowed list of your system’s firewall”
-
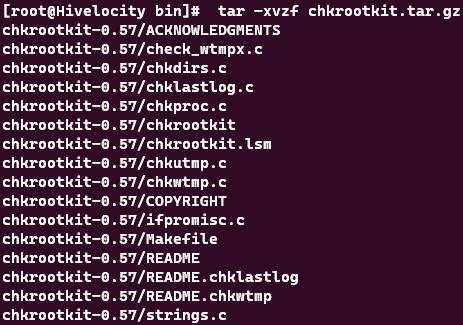
Next, unpack the tarball using the command:
tar -xvzf chkrootkit.tar.gz
-
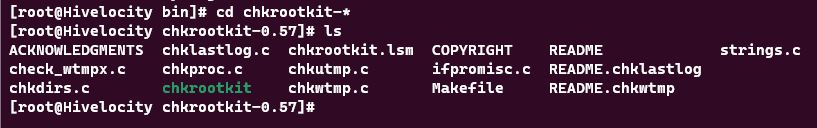
A new directory will be created based on the version of the chkrootkit that we’ve installed. Use the following command to go into whichever directory was created:
cd chkrootkit-*
-
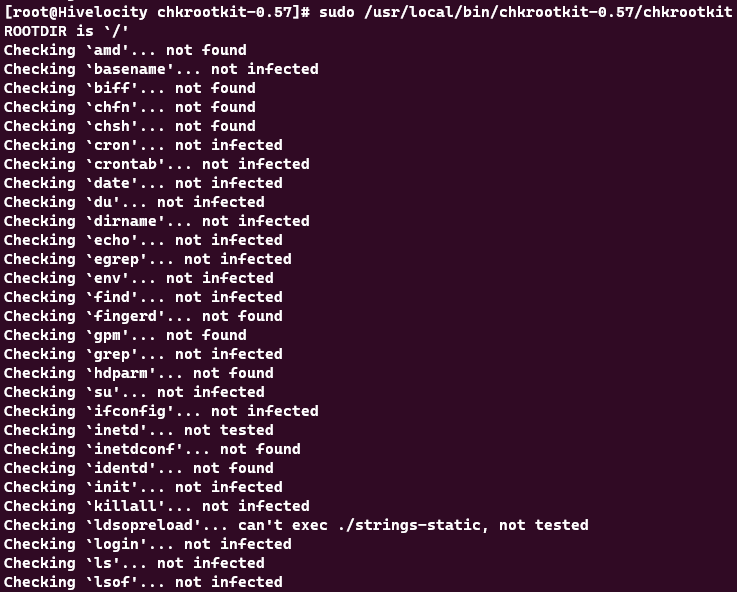
Now that chkrootkit is installed, you can run a scan using the following command. *NOTE: chkrootkit-0.57 in the command below can change based on the version that you have installed.
sudo /usr/local/bin/chkrootkit-0.57/chkrootkit
As a closing note, to have the server checked frequently, a schedule can be made by adding a cron task. For example, you can run the scan every day at 3AM using the following commands:
-
Open the crontab file using the following command:
sudo crontab -e
-
Add the following line,
* 3 * * * /usr/local/bin/chkrootkit >> /chkrootkit_results.txt
Save the file and exit to complete the task. Note that the chkrootkit_results.txt file will have results added daily to the file so make sure it doesn’t grow too big. You can also change the frequency from daily to weekly on Sunday at Midnight using:
* 0 * * 0 /usr/local/bin/chkrootkit >> /chkrootkit_results.txt
*NOTE: Please keep the following in mind when securing your system:
- If a hacker has already gained access, your safest recourse is to wipe the box, re-install the operating system, and restore from a backup that was made prior to the hack.
- Security must be done in layers to be the most effective. You should start off with as many layers as you are comfortable managing and monitoring; and then add layers as they either become available, you see the pattern to make one, etc.
- Security must be an ongoing concern. You don’t just add on the layers (tighten the hatches), and walk away from the ship. You have to manage it several times a day for as long as the server is connected to the Internet.